
Click here to go see the bonus panel!
Hovertext:
I'll just note that I'm posting this comic several hours late because I had to turn in a manuscript that was due 6 months ago.
Today's News:

Hovertext:
I'll just note that I'm posting this comic several hours late because I had to turn in a manuscript that was due 6 months ago.
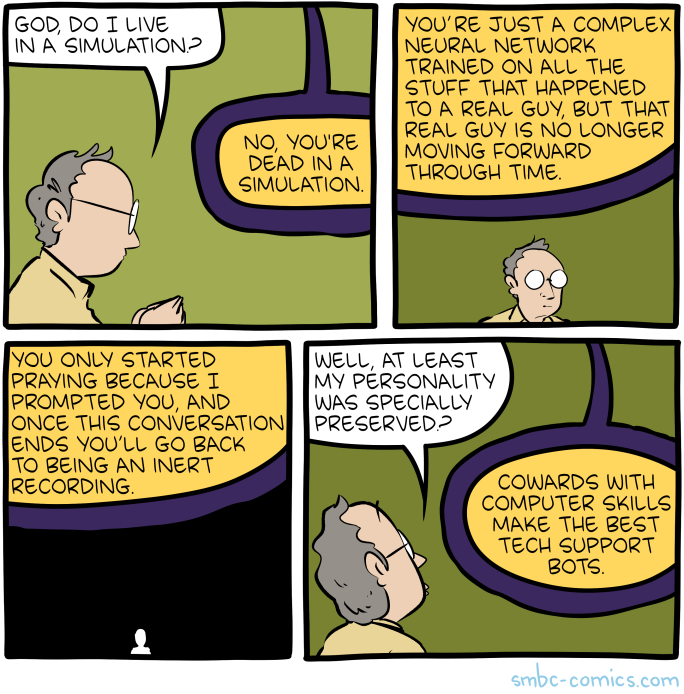
Hovertext:
'It's okay,' God assured him. 'I was automated years ago too.'
Hey Austin, come see me at UT. 1:30pm April 5 2024 RLP 1.302E. I'll be talking space!
Thanks to everyone who bought stuff from the store! ![]() I’m getting more ‘Another Day Another Tuna’ stickers in stock ASAP!
I’m getting more ‘Another Day Another Tuna’ stickers in stock ASAP!
![]() Also I’m posting the final six pages of the latest Plucked Up story to my patreon this weekend! Just need to finish drawing it first!
Also I’m posting the final six pages of the latest Plucked Up story to my patreon this weekend! Just need to finish drawing it first!
![]() Title thanks to stve3000 from the stream!
Title thanks to stve3000 from the stream! ![]()
P.S. the behind-the-scenes pack for patrons will be posted later this weekend! UP NOW!
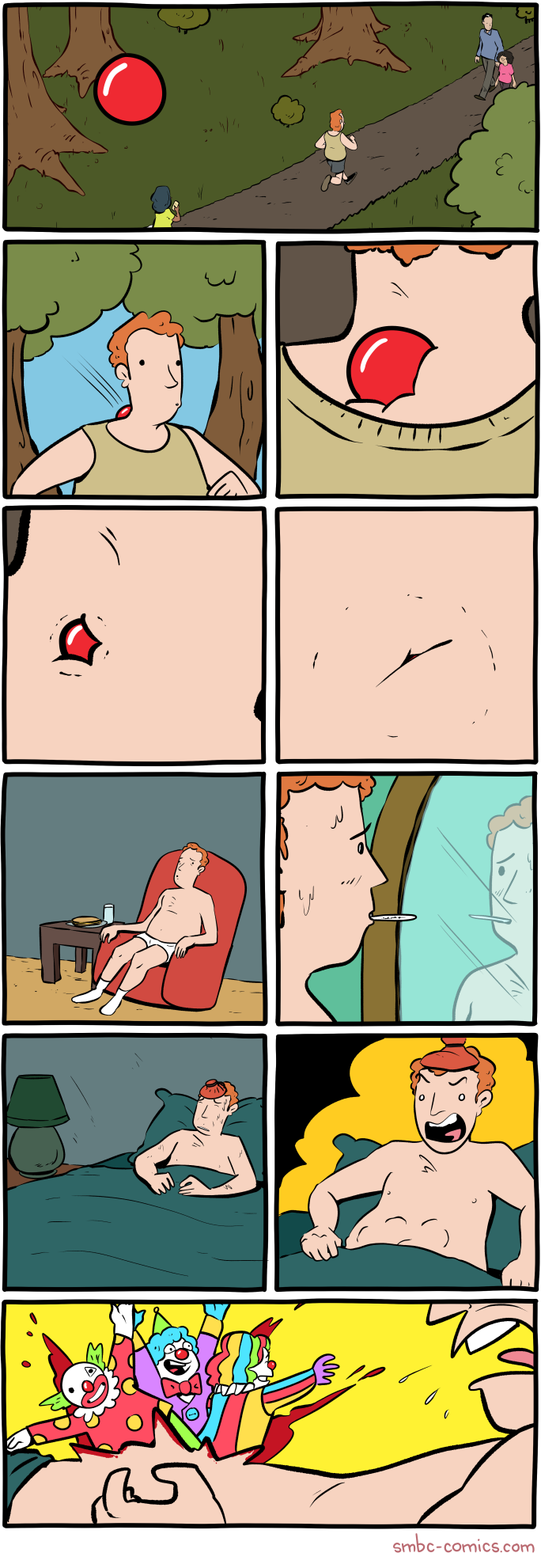
Hovertext:
This is the right opportunity to remind you that every SMBC is available as a high-quality print to adorn your home or office.

And here are some agoraphobic chickens.
Enlarge (credit: Adrienne Bresnahan | Getty Images)
With Ethernet turning 50 this year, Ars is resurfacing this feature on the development and evolution of Ethernet that was originally published in 2011.
Although watching TV shows from the 1970s suggests otherwise, the era wasn't completely devoid of all things resembling modern communication systems. Sure, the 50Kbps modems that the ARPANET ran on were the size of refrigerators, and the widely used Bell 103 modems only transferred 300 bits per second. But long-distance digital communication was common enough, relative to the number of computers deployed. Terminals could also be hooked up to mainframe and minicomputers over relatively short distances with simple serial lines or with more complex multidrop systems. This was all well known; what was new in the '70s was the local area network (LAN). But how to connect all these machines?
The point of a LAN is to connect many more than just two systems, so a simple cable back and forth doesn't get the job done. Connecting several thousands of computers to a LAN can in theory be done using a star, a ring, or a bus topology. A star is obvious enough: every computer is connected to some central point. A bus consists of a single, long cable that computers connect to along its run. With a ring, a cable runs from the first computer to the second, from there to the third and so on until all participating systems are connected, and then the last is connected to the first, completing the ring.
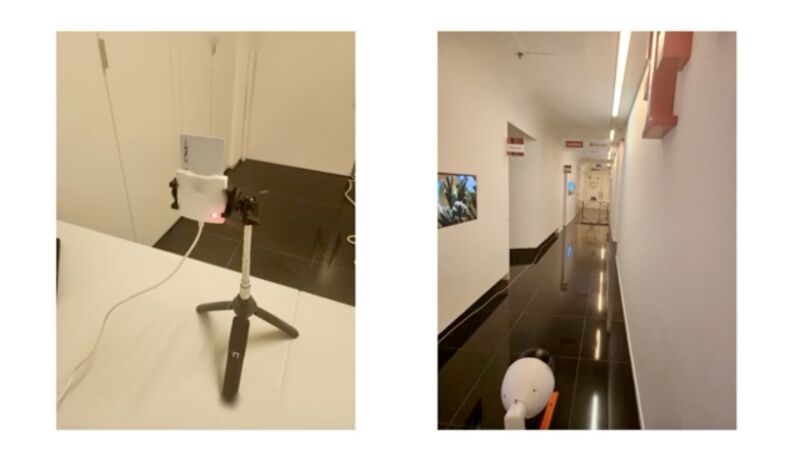
Enlarge / Left: a smart card reader processing the encryption key of an inserted smart card. Right: a surveillance camera video records the reader's power LED from 60 feet away. (credit: Nassi et al.)
Researchers have devised a novel attack that recovers the secret encryption keys stored in smart cards and smartphones by using cameras in iPhones or commercial surveillance systems to video record power LEDs that show when the card reader or smartphone is turned on.
The attacks enable a new way to exploit two previously disclosed side channels, a class of attack that measures physical effects that leak from a device as it performs a cryptographic operation. By carefully monitoring characteristics such as power consumption, sound, electromagnetic emissions, or the amount of time it takes for an operation to occur, attackers can assemble enough information to recover secret keys that underpin the security and confidentiality of a cryptographic algorithm.
As Wired reported in 2008, one of the oldest known side channels was in a top-secret encrypted teletype terminal that the US Army and Navy used during World War II to transmit communications that couldn’t be read by German and Japanese spies. To the surprise of the Bell Labs engineers who designed the terminal, it caused readings from a nearby oscilloscope each time an encrypted letter was entered. While the encryption algorithm in the device was sound, the electromagnetic emissions emanating from the device were enough to provide a side channel that leaked the secret key.

Hovertext:
It turns out if you switch to the one that definitely for sure has a ferrari you might be worse off because there is information embedded in...
Hovertext:
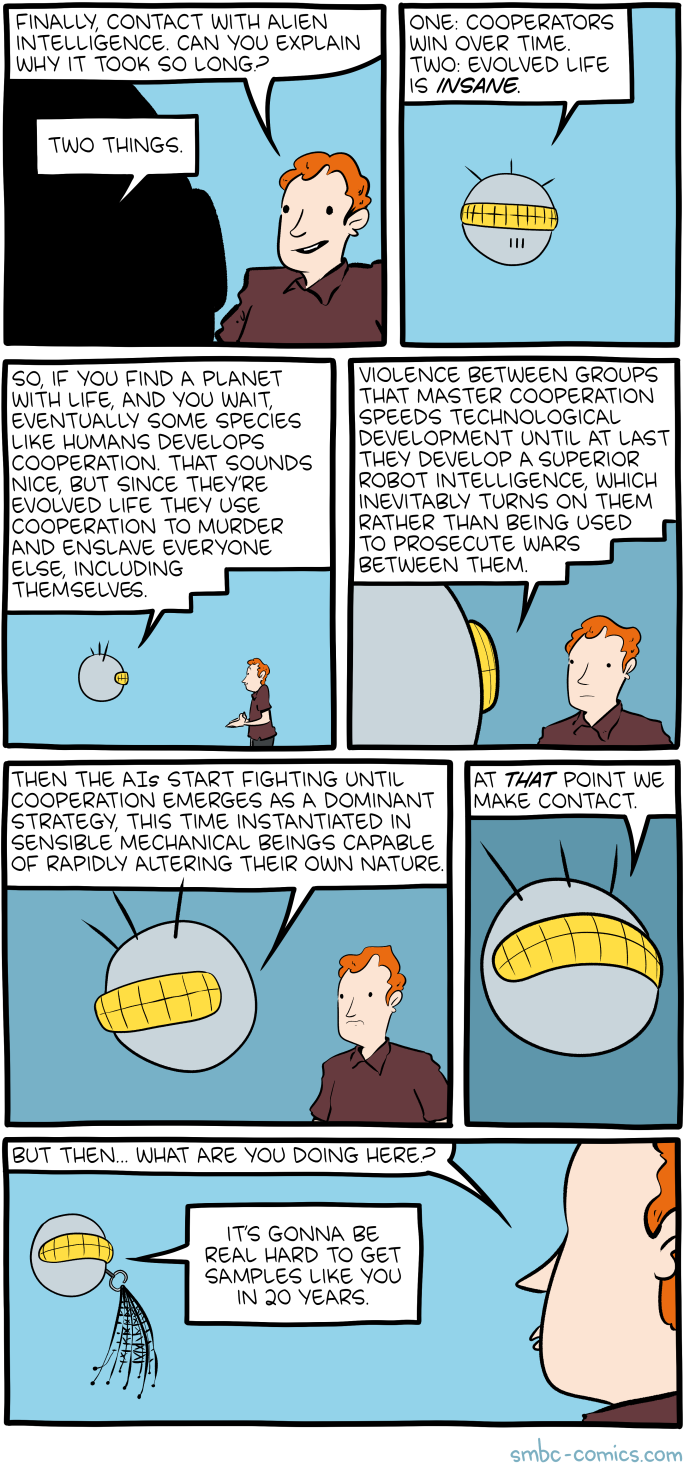
Cooperation is when we hurt people together!
Hovertext:
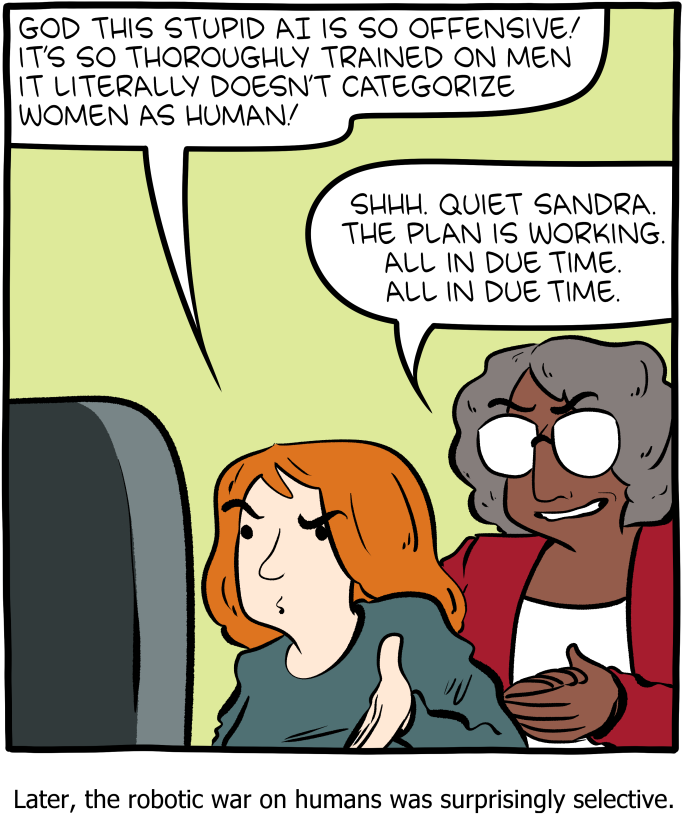
I'm slightly regretting not having this as the twist ending to a comedic novel. Gimme a few years.
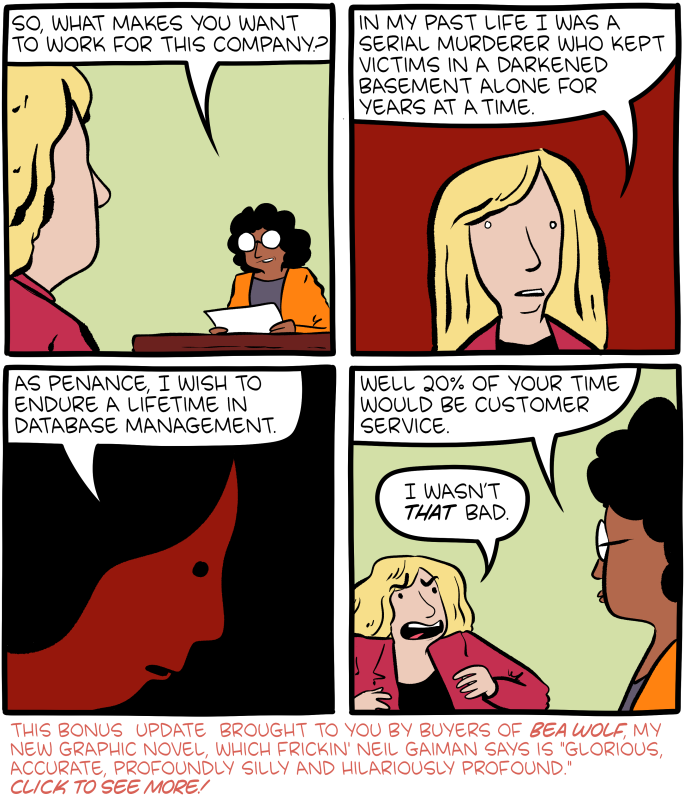
One week until BEA WOLF DAY!
Hovertext:
This is just a big thank you to Bea Wolf buyers. We're already in our 3rd printing and it doesn't come out for a month. If you want a hardcover, lock it in soon - they're gorgeous :D
Thanks y'all, I mean it. Here's one more heartmelting review:
"An instant classic. Like nothing I have ever seen. The unforgettable characters within Treeheart and their death-defying (and extremely funny) heroics now have a permanent place in my brain. This combination of impossibly charming art and boundlessly thrilling and hilarious text is a required addition to your family's library. I love this so much."
â Nathan Pyle